github.com/argoproj/argo-cd@v1.8.7/docs/operator-manual/user-management/openunison.md (about) 1 # OpenUnison 2 3 ## Integrating OpenUnison and ArgoCD 4 5 These instructions will take your through the steps of integrating OpenUnison and ArgoCD to support single sign-on and add a "badge" to your OpenUnison portal to create a single access point for both Kubernetes and ArgoCD. These instructions assume you'll be using both ArgoCD's web interface and command line interface. These instructions assume you are running [OpenUnison 1.0.20+](https://www.tremolosecurity.com/products/orchestra-for-kubernetes). 6 7 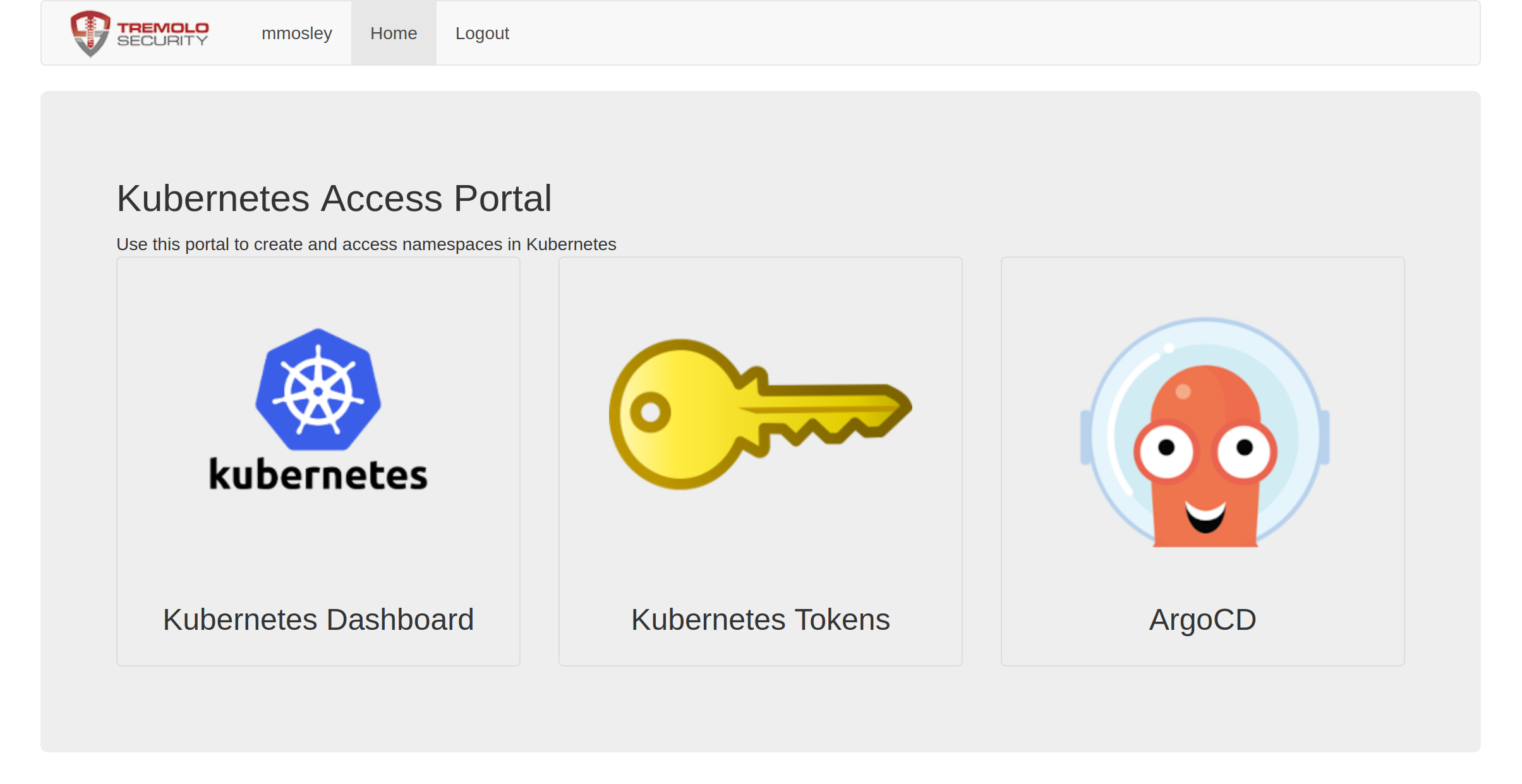 8 9 ## Create an OpenUnison Trust 10 11 Update the below `Trust` object and add it to the `openunison` namespace. The only change you need to make is to replace `argocd.apps.domain.com` with the host name of your ArgoCD URL. The localhost URL is needed for the cli to work. There is no client secret used for ArgoCD since the cli will not work with it. 12 13 ``` 14 apiVersion: openunison.tremolo.io/v1 15 kind: Trust 16 metadata: 17 name: argocd 18 namespace: openunison 19 spec: 20 accessTokenSkewMillis: 120000 21 accessTokenTimeToLive: 1200000 22 authChainName: LoginService 23 clientId: argocd 24 codeLastMileKeyName: lastmile-oidc 25 codeTokenSkewMilis: 60000 26 publicEndpoint: true 27 redirectURI: 28 - https://argocd.apps.domain.com/auth/callback 29 - http://localhost:8085/auth/callback 30 signedUserInfo: true 31 verifyRedirect: true 32 ``` 33 34 ## Create a "Badge" in OpenUnison 35 36 Download [the yaml for a `PortalUrl` object](../../assets/openunison-argocd-url.yaml) and update the `url` to point to your ArgoCD instance. Add the updated `PortalUrl` to the `openunison` namespace of your cluster. 37 38 ## Configure SSO in ArgoCD 39 40 Next, update the `argocd-cm` ConfigMap in the `argocd` namespace. Add the `url` and `oidc.config` sections as seen below. Update `issuer` with the host for OpenUnison. 41 42 ``` 43 apiVersion: v1 44 kind: ConfigMap 45 metadata: 46 name: argocd-cm 47 data: 48 url: https://argocd.apps.domain.com 49 oidc.config: |- 50 name: OpenUnison 51 issuer: https://k8sou.apps.192-168-2-144.nip.io/auth/idp/k8sIdp 52 clientID: argocd 53 requestedScopes: ["openid", "profile", "email", "groups"] 54 ``` 55 56 If everything went correctly, login to your OpenUnison instance and there should be a badge for ArgoCD. Clicking on that badge opens ArgoCD in a new window, already logged in! Additionally, launching the argocd cli tool will launch a browser to login to OpenUnison. 57 58 ## Configure ArgoCD Policy 59 60 OpenUnison places groups in the `groups` claim. These claims will show up when you click on the user-info section of the ArgoCD portal. If you're using LDAP, Active Directory, or Active Directory Federation Services the groups will provided to ArgoCD as full Distinguished Names (DN). Since a DN containers commas (`,`) you'll need to quote the group name in your policy. For instance to assign `CN=k8s_login_cluster_admins,CN=Users,DC=ent2k12,DC=domain,DC=com` as an administrator would look like: 61 62 ``` 63 apiVersion: v1 64 kind: ConfigMap 65 metadata: 66 name: argocd-rbac-cm 67 namespace: argocd 68 data: 69 policy.csv: | 70 g, "CN=k8s_login_cluster_admins,CN=Users,DC=ent2k12,DC=domain,DC=com", role:admin 71 ```