github.com/osdi23p228/fabric@v0.0.0-20221218062954-77808885f5db/docs/source/network/network.md (about) 1 # Blockchain network 2 3 This topic will describe, **at a conceptual level**, how Hyperledger Fabric 4 allows organizations to collaborate in the formation of blockchain networks. If 5 you're an architect, administrator or developer, you can use this topic to get a 6 solid understanding of the major structure and process components in a 7 Hyperledger Fabric blockchain network. This topic will use a manageable worked 8 example that introduces all of the major components in a blockchain network. 9 10 After reading this topic and understanding the concept of policies, you will 11 have a solid understanding of the decisions that organizations need to make to 12 establish the policies that control a deployed Hyperledger Fabric network. 13 You'll also understand how organizations manage network evolution using 14 declarative policies -- a key feature of Hyperledger Fabric. In a nutshell, 15 you'll understand the major technical components of Hyperledger Fabric and the 16 decisions organizations need to make about them. 17 18 ## What is a blockchain network? 19 20 A blockchain network is a technical infrastructure that provides ledger and 21 smart contract (chaincode) services to applications. Primarily, smart contracts 22 are used to generate transactions which are subsequently distributed to every 23 peer node in the network where they are immutably recorded on their copy of the 24 ledger. The users of applications might be end users using client applications 25 or blockchain network administrators. 26 27 In most cases, multiple [organizations](../glossary.html#organization) come 28 together as a [consortium](../glossary.html#consortium) to form the network and 29 their permissions are determined by a set of [policies](../glossary.html#policy) 30 that are agreed by the consortium when the network is originally configured. 31 Moreover, network policies can change over time subject to the agreement of the 32 organizations in the consortium, as we'll discover when we discuss the concept 33 of *modification policy*. 34 35 ## The sample network 36 37 Before we start, let's show you what we're aiming at! Here's a diagram 38 representing the **final state** of our sample network. 39 40 Don't worry that this might look complicated! As we go through this topic, we 41 will build up the network piece by piece, so that you see how the organizations 42 R1, R2, R3 and R4 contribute infrastructure to the network to help form it. This 43 infrastructure implements the blockchain network, and it is governed by policies 44 agreed by the organizations who form the network -- for example, who can add new 45 organizations. You'll discover how applications consume the ledger and smart 46 contract services provided by the blockchain network. 47 48 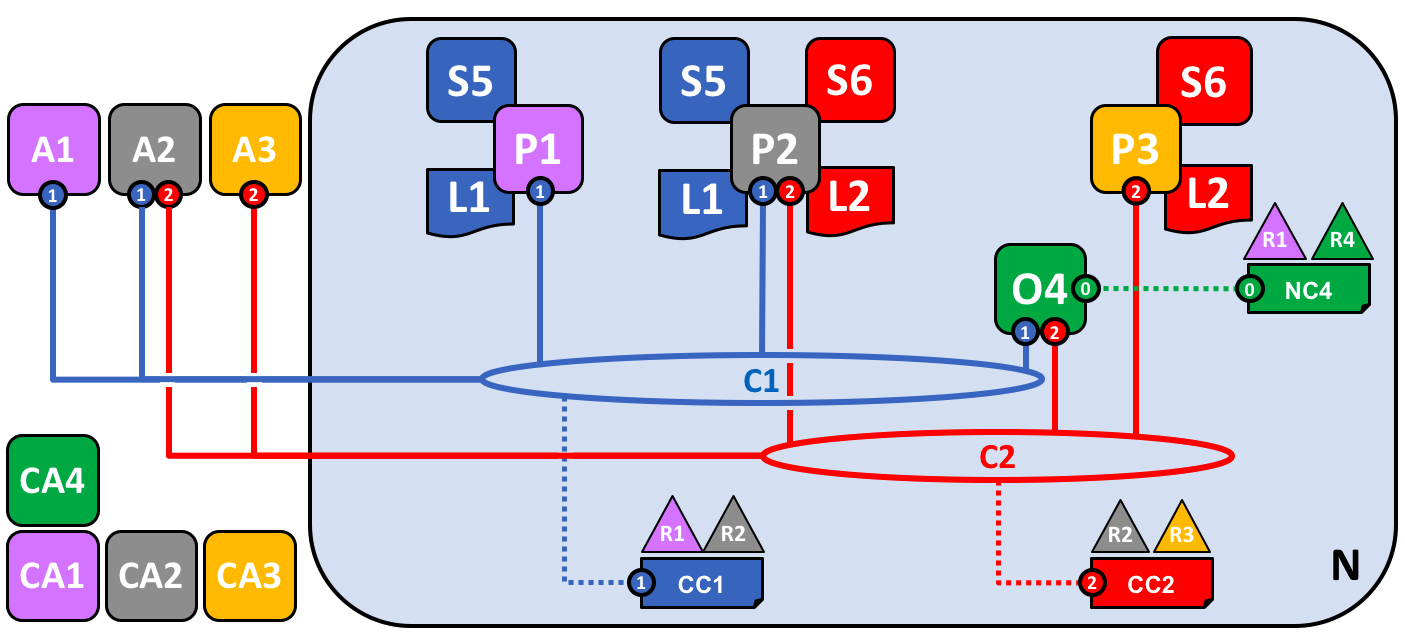 49 50 *Four organizations, R1, R2, R3 and R4 have jointly decided, and written into an 51 agreement, that they will set up and exploit a Hyperledger Fabric 52 network. R4 has been assigned to be the network initiator -- it has been given 53 the power to set up the initial version of the network. R4 has no intention to 54 perform business transactions on the network. R1 and R2 have a need for a 55 private communications within the overall network, as do R2 and R3. 56 Organization R1 has a client application that can perform business transactions 57 within channel C1. Organization R2 has a client application that can do similar 58 work both in channel C1 and C2. Organization R3 has a client application that 59 can do this on channel C2. Peer node P1 maintains a copy of the ledger L1 60 associated with C1. Peer node P2 maintains a copy of the ledger L1 associated 61 with C1 and a copy of ledger L2 associated with C2. Peer node P3 maintains a 62 copy of the ledger L2 associated with C2. The network is governed according to 63 policy rules specified in network configuration NC4, the network is under the 64 control of organizations R1 and R4. Channel C1 is governed according to the 65 policy rules specified in channel configuration CC1; the channel is under the 66 control of organizations R1 and R2. Channel C2 is governed according to the 67 policy rules specified in channel configuration CC2; the channel is under the 68 control of organizations R2 and R3. There is an ordering service O4 that 69 services as a network administration point for N, and uses the system channel. 70 The ordering service also supports application channels C1 and C2, for the 71 purposes of transaction ordering into blocks for distribution. Each of the four 72 organizations has a preferred Certificate Authority.* 73 74 ## Creating the Network 75 76 Let's start at the beginning by creating the basis for the network: 77 78  79 80 *The network is formed when an orderer is started. In our example network, N, 81 the ordering service comprising a single node, O4, is configured according to a 82 network configuration NC4, which gives administrative rights to organization 83 R4. At the network level, Certificate Authority CA4 is used to dispense 84 identities to the administrators and network nodes of the R4 organization.* 85 86 We can see that the first thing that defines a **network, N,** is an **ordering 87 service, O4**. It's helpful to think of the ordering service as the initial 88 administration point for the network. As agreed beforehand, O4 is initially 89 configured and started by an administrator in organization R4, and hosted in R4. 90 The configuration NC4 contains the policies that describe the starting set of 91 administrative capabilities for the network. Initially this is set to only give 92 R4 rights over the network. This will change, as we'll see later, but for now R4 93 is the only member of the network. 94 95 ### Certificate Authorities 96 97 You can also see a Certificate Authority, CA4, which is used to issue 98 certificates to administrators and network nodes. CA4 plays a key role in our 99 network because it dispenses X.509 certificates that can be used to identify 100 components as belonging to organization R4. Certificates issued by CAs 101 can also be used to sign transactions to indicate that an organization endorses 102 the transaction result -- a precondition of it being accepted onto the 103 ledger. Let's examine these two aspects of a CA in a little more detail. 104 105 Firstly, different components of the blockchain network use certificates to 106 identify themselves to each other as being from a particular organization. 107 That's why there is usually more than one CA supporting a blockchain network -- 108 different organizations often use different CAs. We're going to use four CAs in 109 our network; one for each organization. Indeed, CAs are so important that 110 Hyperledger Fabric provides you with a built-in one (called *Fabric-CA*) to help 111 you get going, though in practice, organizations will choose to use their own 112 CA. 113 114 The mapping of certificates to member organizations is achieved by via 115 a structure called a 116 [Membership Services Provider (MSP)](../glossary.html#membership-services). 117 Network configuration NC4 uses a named 118 MSP to identify the properties of certificates dispensed by CA4 which associate 119 certificate holders with organization R4. NC4 can then use this MSP name in 120 policies to grant actors from R4 particular 121 rights over network resources. An example of such a policy is to identify the 122 administrators in R4 who can add new member organizations to the network. We 123 don't show MSPs on these diagrams, as they would just clutter them up, but they 124 are very important. 125 126 Secondly, we'll see later how certificates issued by CAs are at the heart of the 127 [transaction](../glossary.html#transaction) generation and validation process. 128 Specifically, X.509 certificates are used in client application 129 [transaction proposals](../glossary.html#proposal) and smart contract 130 [transaction responses](../glossary.html#response) to digitally sign 131 [transactions](../glossary.html#transaction). Subsequently the network nodes 132 who host copies of the ledger verify that transaction signatures are valid 133 before accepting transactions onto the ledger. 134 135 Let's recap the basic structure of our example blockchain network. There's a 136 resource, the network N, accessed by a set of users defined by a Certificate 137 Authority CA4, who have a set of rights over the resources in the network N as 138 described by policies contained inside a network configuration NC4. All of this 139 is made real when we configure and start the ordering service node O4. 140 141 ## Adding Network Administrators 142 143 NC4 was initially configured to only allow R4 users administrative rights over 144 the network. In this next phase, we are going to allow organization R1 users to 145 administer the network. Let's see how the network evolves: 146 147  148 149 *Organization R4 updates the network configuration to make organization R1 an 150 administrator too. After this point R1 and R4 have equal rights over the 151 network configuration.* 152 153 We see the addition of a new organization R1 as an administrator -- R1 and R4 154 now have equal rights over the network. We can also see that certificate 155 authority CA1 has been added -- it can be used to identify users from the R1 156 organization. After this point, users from both R1 and R4 can administer the 157 network. 158 159 Although the orderer node, O4, is running on R4's infrastructure, R1 has shared 160 administrative rights over it, as long as it can gain network access. It means 161 that R1 or R4 could update the network configuration NC4 to allow the R2 162 organization a subset of network operations. In this way, even though R4 is 163 running the ordering service, and R1 has full administrative rights over it, R2 164 has limited rights to create new consortia. 165 166 In its simplest form, the ordering service is a single node in the network, and 167 that's what you can see in the example. Ordering services are usually 168 multi-node, and can be configured to have different nodes in different 169 organizations. For example, we might run O4 in R4 and connect it to O2, a 170 separate orderer node in organization R1. In this way, we would have a 171 multi-site, multi-organization administration structure. 172 173 We'll discuss the ordering service a little [later in this topic](#the-ordering-service), 174 but for now just think of the ordering service as an administration point which 175 provides different organizations controlled access to the network. 176 177 ## Defining a Consortium 178 179 Although the network can now be administered by R1 and R4, there is very little 180 that can be done. The first thing we need to do is define a consortium. This 181 word literally means "a group with a shared destiny", so it's an appropriate 182 choice for a set of organizations in a blockchain network. 183 184 Let's see how a consortium is defined: 185 186  187 188 *A network administrator defines a consortium X1 that contains two members, 189 the organizations R1 and R2. This consortium definition is stored in the 190 network configuration NC4, and will be used at the next stage of network 191 development. CA1 and CA2 are the respective Certificate Authorities for these 192 organizations.* 193 194 Because of the way NC4 is configured, only R1 or R4 can create new consortia. 195 This diagram shows the addition of a new consortium, X1, which defines R1 and R2 196 as its constituting organizations. We can also see that CA2 has been added to 197 identify users from R2. Note that a consortium can have any number of 198 organizational members -- we have just shown two as it is the simplest 199 configuration. 200 201 Why are consortia important? We can see that a consortium defines the set of 202 organizations in the network who share a need to **transact** with one another -- 203 in this case R1 and R2. It really makes sense to group organizations together if 204 they have a common goal, and that's exactly what's happening. 205 206 The network, although started by a single organization, is now controlled by a 207 larger set of organizations. We could have started it this way, with R1, R2 and 208 R4 having shared control, but this build up makes it easier to understand. 209 210 We're now going to use consortium X1 to create a really important part of a 211 Hyperledger Fabric blockchain -- **a channel**. 212 213 ## Creating a channel for a consortium 214 215 So let's create this key part of the Fabric blockchain network -- **a channel**. 216 A channel is a primary communications mechanism by which the members of a 217 consortium can communicate with each other. There can be multiple channels in a 218 network, but for now, we'll start with one. 219 220 Let's see how the first channel has been added to the network: 221 222 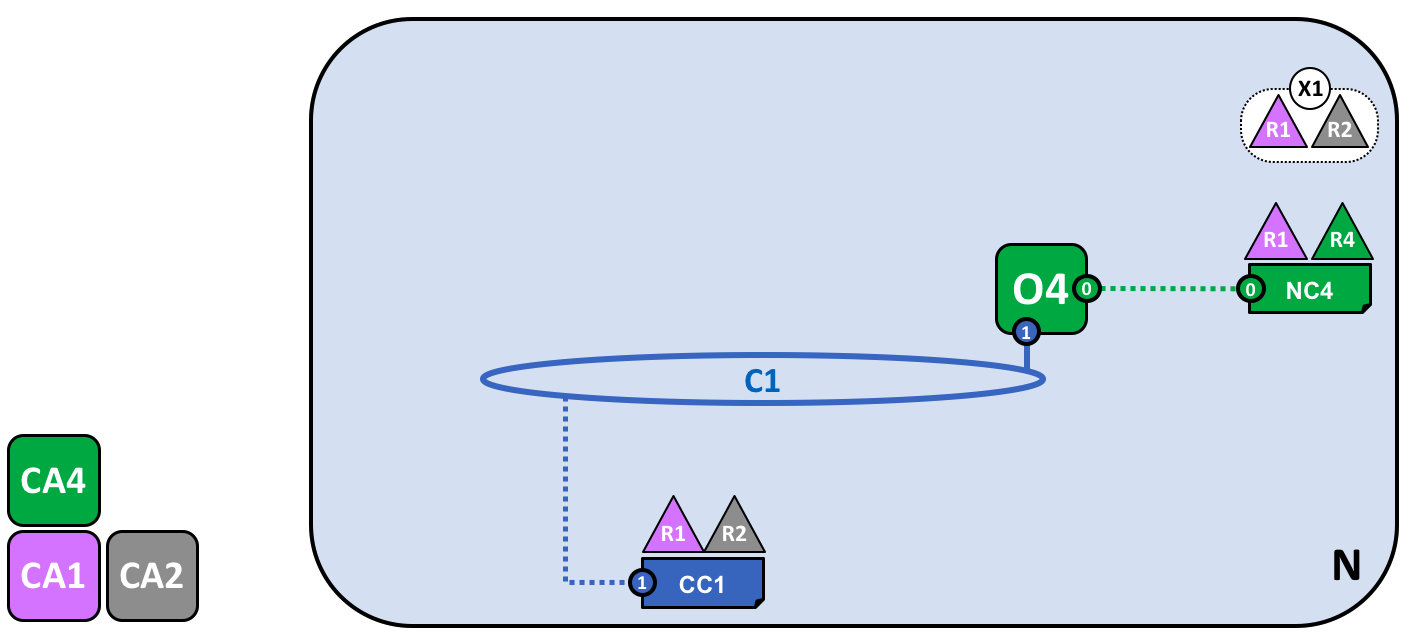 223 224 *A channel C1 has been created for R1 and R2 using the consortium definition X1. 225 The channel is governed by a channel configuration CC1, completely separate to 226 the network configuration. CC1 is managed by R1 and R2 who have equal rights 227 over C1. R4 has no rights in CC1 whatsoever.* 228 229 The channel C1 provides a private communications mechanism for the consortium 230 X1. We can see channel C1 has been connected to the ordering service O4 but that 231 nothing else is attached to it. In the next stage of network development, we're 232 going to connect components such as client applications and peer nodes. But at 233 this point, a channel represents the **potential** for future connectivity. 234 235 Even though channel C1 is a part of the network N, it is quite distinguishable 236 from it. Also notice that organizations R3 and R4 are not in this channel -- it 237 is for transaction processing between R1 and R2. In the previous step, we saw 238 how R4 could grant R1 permission to create new consortia. It's helpful to 239 mention that R4 **also** allowed R1 to create channels! In this diagram, it 240 could have been organization R1 or R4 who created a channel C1. Again, note 241 that a channel can have any number of organizations connected to it -- we've 242 shown two as it's the simplest configuration. 243 244 Again, notice how channel C1 has a completely separate configuration, CC1, to 245 the network configuration NC4. CC1 contains the policies that govern the 246 rights that R1 and R2 have over the channel C1 -- and as we've seen, R3 and 247 R4 have no permissions in this channel. R3 and R4 can only interact with C1 if 248 they are added by R1 or R2 to the appropriate policy in the channel 249 configuration CC1. An example is defining who can add a new organization to the 250 channel. Specifically, note that R4 cannot add itself to the channel C1 -- it 251 must, and can only, be authorized by R1 or R2. 252 253 Why are channels so important? Channels are useful because they provide a 254 mechanism for private communications and private data between the members of a 255 consortium. Channels provide privacy from other channels, and from the network. 256 Hyperledger Fabric is powerful in this regard, as it allows organizations to 257 share infrastructure and keep it private at the same time. There's no 258 contradiction here -- different consortia within the network will have a need 259 for different information and processes to be appropriately shared, and channels 260 provide an efficient mechanism to do this. Channels provide an efficient 261 sharing of infrastructure while maintaining data and communications privacy. 262 263 We can also see that once a channel has been created, it is in a very real sense 264 "free from the network". It is only organizations that are explicitly specified 265 in a channel configuration that have any control over it, from this time forward 266 into the future. Likewise, any updates to network configuration NC4 from this 267 time onwards will have no direct effect on channel configuration CC1; for 268 example if consortia definition X1 is changed, it will not affect the members of 269 channel C1. Channels are therefore useful because they allow private 270 communications between the organizations constituting the channel. Moreover, the 271 data in a channel is completely isolated from the rest of the network, including 272 other channels. 273 274 As an aside, there is also a special **system channel** defined for use by the 275 ordering service. It behaves in exactly the same way as a regular channel, 276 which are sometimes called **application channels** for this reason. We don't 277 normally need to worry about this channel, but we'll discuss a little bit more 278 about it [later in this topic](#the-ordering-service). 279 280 ## Peers and Ledgers 281 282 Let's now start to use the channel to connect the blockchain network and the 283 organizational components together. In the next stage of network development, we 284 can see that our network N has just acquired two new components, namely a peer 285 node P1 and a ledger instance, L1. 286 287  288 289 *A peer node P1 has joined the channel C1. P1 physically hosts a copy of the 290 ledger L1. P1 and O4 can communicate with each other using channel C1.* 291 292 Peer nodes are the network components where copies of the blockchain ledger are 293 hosted! At last, we're starting to see some recognizable blockchain components! 294 P1's purpose in the network is purely to host a copy of the ledger L1 for others 295 to access. We can think of L1 as being **physically hosted** on P1, but 296 **logically hosted** on the channel C1. We'll see this idea more clearly when we 297 add more peers to the channel. 298 299 A key part of a P1's configuration is an X.509 identity issued by CA1 which 300 associates P1 with organization R1. When R1 administrator takes the 301 action of joining peer P1 to channel C1, and the peer starts pulling blocks from 302 the orderer O4, the orderer uses the channel configuration 303 CC1 to determine P1's permissions on this channel. For example, policy in CC1 304 determines whether P1 (or the organization R1) can read and/or write on the 305 channel C1. 306 307 Notice how peers are joined to channels by the organizations that own them, and 308 though we've only added one peer, we'll see how there can be multiple peer 309 nodes on multiple channels within the network. We'll see the different roles 310 that peers can take on a little later. 311 312 ## Applications and Smart Contract chaincode 313 314 Now that the channel C1 has a ledger on it, we can start connecting client 315 applications to consume some of the services provided by workhorse of the 316 ledger, the peer! 317 318 Notice how the network has grown: 319 320  321 322 *A smart contract S5 has been installed onto P1. Client application A1 in 323 organization R1 can use S5 to access the ledger via peer node P1. A1, P1 and 324 O4 are all joined to channel C1, i.e. they can all make use of the 325 communication facilities provided by that channel.* 326 327 In the next stage of network development, we can see that client application A1 328 can use channel C1 to connect to specific network resources -- in this case A1 329 can connect to both peer node P1 and orderer node O4. Again, see how channels 330 are central to the communication between network and organization components. 331 Just like peers and orderers, a client application will have an identity that 332 associates it with an organization. In our example, client application A1 is 333 associated with organization R1; and although it is outside the Fabric 334 blockchain network, it is connected to it via the channel C1. 335 336 It might now appear that A1 can access the ledger L1 directly via P1, but in 337 fact, all access is managed via a special program called a smart contract 338 chaincode, S5. Think of S5 as defining all the common access patterns to the 339 ledger; S5 provides a well-defined set of ways by which the ledger L1 can 340 be queried or updated. In short, client application A1 has to go through smart 341 contract S5 to get to ledger L1! 342 343 Smart contracts can be created by application developers in each organization to 344 implement a business process shared by the consortium members. Smart contracts 345 are used to help generate transactions which can be subsequently distributed to 346 every node in the network. We'll discuss this idea a little later; it'll be 347 easier to understand when the network is bigger. For now, the important thing to 348 understand is that to get to this point two operations must have been performed 349 on the smart contract; it must have been **installed** on peers, and then 350 **defined** on a channel. 351 352 Hyperledger Fabric users often use the terms **smart contract** and 353 **chaincode** interchangeably. In general, a smart contract defines the 354 **transaction logic** that controls the lifecycle of a business object contained 355 in the world state. It is then packaged into a chaincode which is then deployed 356 to a blockchain network. Think of smart contracts as governing transactions, 357 whereas chaincode governs how smart contracts are packaged for deployment. 358 359 ### Installing a chaincode package 360 361 After a smart contract S5 has been developed, an administrator in organization 362 R1 must create a chaincode package and [install](../glossary.html#install) it 363 onto peer node P1. This is a straightforward operation; once completed, P1 has 364 full knowledge of S5. Specifically, P1 can see the **implementation** logic of 365 S5 -- the program code that it uses to access the ledger L1. We contrast this to 366 the S5 **interface** which merely describes the inputs and outputs of S5, 367 without regard to its implementation. 368 369 When an organization has multiple peers in a channel, it can choose the peers 370 upon which it installs smart contracts; it does not need to install a smart 371 contract on every peer. 372 373 ### Defining a chaincode 374 375 Although a chaincode is installed on the peers of individual organizations, it 376 is governed and operated in the scope of a channel. Each organization needs to 377 approve a **chaincode definition**, a set of parameters that establish how a 378 chaincode will be used on a channel. An organization must approve a chaincode 379 definition in order to use the installed smart contract to query the ledger 380 and endorse transactions. In our example, which only has a single peer node P1, 381 an administrator in organization R1 must approve a chaincode definition for S5. 382 383 A sufficient number of organizations need to approve a chaincode definition (A 384 majority, by default) before the chaincode definition can be committed to the 385 channel and used to interact with the channel ledger. Because the channel only 386 has one member, the administrator of R1 can commit the chaincode definition of 387 S5 to the channel C1. Once the definition has been committed, S5 can now be 388 [invoked](../glossary.html#invoke) by client application A1! 389 390 Note that although every component on the channel can now access S5, they are 391 not able to see its program logic. This remains private to those nodes who have 392 installed it; in our example that means P1. Conceptually this means that it's 393 the smart contract **interface** that is defined and committed to a channel, in 394 contrast to the smart contract **implementation** that is installed. To reinforce 395 this idea; installing a smart contract shows how we think of it being 396 **physically hosted** on a peer, whereas a smart contract that has been defined 397 on a channel shows how we consider it **logically hosted** by the channel. 398 399 ### Endorsement policy 400 401 The most important piece of information supplied within the chaincode definition 402 is the [endorsement policy](../glossary.html#endorsement-policy). It describes 403 which organizations must approve transactions before they will be accepted by other 404 organizations onto their copy of the ledger. In our sample network, transactions 405 can only be accepted onto ledger L1 if R1 or R2 endorse them. 406 407 Committing the chaincode definition to the channel places the endorsement policy 408 on the channel ledger; it enables it to be accessed by any member of the channel. 409 You can read more about endorsement policies in the [transaction flow topic](../txflow.html). 410 411 ### Invoking a smart contract 412 413 Once a smart contract has been installed on a peer node and defined on a 414 channel it can be [invoked](../glossary.html#invoke) by a client application. 415 Client applications do this by sending transaction proposals to peers owned by 416 the organizations specified by the smart contract endorsement policy. The 417 transaction proposal serves as input to the smart contract, which uses it to 418 generate an endorsed transaction response, which is returned by the peer node to 419 the client application. 420 421 It's these transactions responses that are packaged together with the 422 transaction proposal to form a fully endorsed transaction, which can be 423 distributed to the entire network. We'll look at this in more detail later For 424 now, it's enough to understand how applications invoke smart contracts to 425 generate endorsed transactions. 426 427 By this stage in network development we can see that organization R1 is fully 428 participating in the network. Its applications -- starting with A1 -- can access 429 the ledger L1 via smart contract S5, to generate transactions that will be 430 endorsed by R1, and therefore accepted onto the ledger because they conform to 431 the endorsement policy. 432 433 ## Network completed 434 435 Recall that our objective was to create a channel for consortium X1 -- 436 organizations R1 and R2. This next phase of network development sees 437 organization R2 add its infrastructure to the network. 438 439 Let's see how the network has evolved: 440 441  442 443 *The network has grown through the addition of infrastructure from 444 organization R2. Specifically, R2 has added peer node P2, which hosts a copy of 445 ledger L1, and chaincode S5. R2 approves the same chaincode definition as R1. 446 P2 has also joined channel C1, as has application A2. A2 and P2 are identified 447 using certificates from CA2. All of this means that both applications A1 and A2 448 can invoke S5 on C1 either using peer node P1 or P2.* 449 450 We can see that organization R2 has added a peer node, P2, on channel C1. P2 451 also hosts a copy of the ledger L1 and smart contract S5. We can see that R2 has 452 also added client application A2 which can connect to the network via channel 453 C1. To achieve this, an administrator in organization R2 has created peer node 454 P2 and joined it to channel C1, in the same way as an administrator in R1. The 455 administrator also has to approve the same chaincode definition as R1. 456 457 We have created our first operational network! At this stage in network 458 development, we have a channel in which organizations R1 and R2 can fully 459 transact with each other. Specifically, this means that applications A1 and A2 460 can generate transactions using smart contract S5 and ledger L1 on channel C1. 461 462 ### Generating and accepting transactions 463 464 In contrast to peer nodes, which always host a copy of the ledger, we see that 465 there are two different kinds of peer nodes; those which host smart contracts 466 and those which do not. In our network, every peer hosts a copy of the smart 467 contract, but in larger networks, there will be many more peer nodes that do not 468 host a copy of the smart contract. A peer can only *run* a smart contract if it 469 is installed on it, but it can *know* about the interface of a smart contract by 470 being connected to a channel. 471 472 You should not think of peer nodes which do not have smart contracts installed 473 as being somehow inferior. It's more the case that peer nodes with smart 474 contracts have a special power -- to help **generate** transactions. Note that 475 all peer nodes can **validate** and subsequently **accept** or **reject** 476 transactions onto their copy of the ledger L1. However, only peer nodes with a 477 smart contract installed can take part in the process of transaction 478 **endorsement** which is central to the generation of valid transactions. 479 480 We don't need to worry about the exact details of how transactions are 481 generated, distributed and accepted in this topic -- it is sufficient to 482 understand that we have a blockchain network where organizations R1 and R2 can 483 share information and processes as ledger-captured transactions. We'll learn a 484 lot more about transactions, ledgers, smart contracts in other topics. 485 486 ### Types of peers 487 488 In Hyperledger Fabric, while all peers are the same, they can assume multiple 489 roles depending on how the network is configured. We now have enough 490 understanding of a typical network topology to describe these roles. 491 492 * [*Committing peer*](../glossary.html#commitment). Every peer node in a 493 channel is a committing peer. It receives blocks of generated transactions, 494 which are subsequently validated before they are committed to the peer 495 node's copy of the ledger as an append operation. 496 497 * [*Endorsing peer*](../glossary.html#endorsement). Every peer with a smart 498 contract *can* be an endorsing peer if it has a smart contract installed. 499 However, to actually *be* an endorsing peer, the smart contract on the peer 500 must be used by a client application to generate a digitally signed 501 transaction response. The term *endorsing peer* is an explicit reference to 502 this fact. 503 504 An endorsement policy for a smart contract identifies the 505 organizations whose peer should digitally sign a generated transaction 506 before it can be accepted onto a committing peer's copy of the ledger. 507 508 These are the two major types of peer; there are two other roles a peer can 509 adopt: 510 511 * [*Leader peer*](../glossary.html#leading-peer). When an organization has 512 multiple peers in a channel, a leader peer is a node which takes 513 responsibility for distributing transactions from the orderer to the other 514 committing peers in the organization. A peer can choose to participate in 515 static or dynamic leadership selection. 516 517 It is helpful, therefore to think of two sets of peers from leadership 518 perspective -- those that have static leader selection, and those with 519 dynamic leader selection. For the static set, zero or more peers can be 520 configured as leaders. For the dynamic set, one peer will be elected leader 521 by the set. Moreover, in the dynamic set, if a leader peer fails, then the 522 remaining peers will re-elect a leader. 523 524 It means that an organization's peers can have one or more leaders connected 525 to the ordering service. This can help to improve resilience and scalability 526 in large networks which process high volumes of transactions. 527 528 * [*Anchor peer*](../glossary.html#anchor-peer). If a peer needs to 529 communicate with a peer in another organization, then it can use one of the 530 **anchor peers** defined in the channel configuration for that organization. 531 An organization can have zero or more anchor peers defined for it, and an 532 anchor peer can help with many different cross-organization communication 533 scenarios. 534 535 Note that a peer can be a committing peer, endorsing peer, leader peer and 536 anchor peer all at the same time! Only the anchor peer is optional -- for all 537 practical purposes there will always be a leader peer and at least one 538 endorsing peer and at least one committing peer. 539 540 ### Adding organizations and peers to the channel 541 542 When R2 joins the channel, the organization must install smart contract S5 543 onto its peer node, P2. That's obvious -- if applications A1 or A2 wish to use 544 S5 on peer node P2 to generate transactions, it must first be present; 545 installation is the mechanism by which this happens. At this point, peer node P2 546 has a physical copy of the smart contract and the ledger; like P1, it can both 547 generate and accept transactions onto its copy of ledger L1. 548 549 R2 must approve the same chaincode definition as was approved by R1 in order to 550 use smart contract S5. Because the chaincode definition has already been 551 committed to the channel by organization R1, R2 can use the chaincode as soon as 552 the organization approves the chaincode definition and installs the chaincode 553 package. The commit transaction only needs to happen once. A new organization 554 can use the chaincode as soon as they approve the chaincode parameters agreed to 555 by other members of the channel. Because the approval of a chaincode definition 556 occurs at the organization level, R2 can approve the chaincode definition once 557 and join multiple peers to the channel with the chaincode package installed. 558 However, if R2 wanted to change the chaincode definition, both R1 and R2 would 559 need to approve a new definition for their organization, and then one of the 560 organizations would need to commit the definition to the channel. 561 562 In our network, we can see that channel C1 connects two client applications, two 563 peer nodes and an ordering service. Since there is only one channel, there is 564 only one **logical** ledger with which these components interact. Peer nodes P1 565 and P2 have identical copies of ledger L1. Copies of smart contract S5 will 566 usually be identically implemented using the same programming language, but 567 if not, they must be semantically equivalent. 568 569 We can see that the careful addition of peers to the network can help support 570 increased throughput, stability, and resilience. For example, more peers in a 571 network will allow more applications to connect to it; and multiple peers in an 572 organization will provide extra resilience in the case of planned or unplanned 573 outages. 574 575 It all means that it is possible to configure sophisticated topologies which 576 support a variety of operational goals -- there is no theoretical limit to how 577 big a network can get. Moreover, the technical mechanism by which peers within 578 an individual organization efficiently discover and communicate with each other -- 579 the [gossip protocol](../gossip.html#gossip-protocol) -- will accommodate a 580 large number of peer nodes in support of such topologies. 581 582 The careful use of network and channel policies allow even large networks to be 583 well-governed. Organizations are free to add peer nodes to the network so long 584 as they conform to the policies agreed by the network. Network and channel 585 policies create the balance between autonomy and control which characterizes a 586 de-centralized network. 587 588 ## Simplifying the visual vocabulary 589 590 We’re now going to simplify the visual vocabulary used to represent our sample 591 blockchain network. As the size of the network grows, the lines initially used 592 to help us understand channels will become cumbersome. Imagine how complicated 593 our diagram would be if we added another peer or client application, or another 594 channel? 595 596 That's what we're going to do in a minute, so before we do, let's simplify the 597 visual vocabulary. Here's a simplified representation of the network we've 598 developed so far: 599 600  601 602 *The diagram shows the facts relating to channel C1 in the network N as follows: 603 Client applications A1 and A2 can use channel C1 for communication with peers 604 P1 and P2, and orderer O4. Peer nodes P1 and P2 can use the communication 605 services of channel C1. Ordering service O4 can make use of the communication 606 services of channel C1. Channel configuration CC1 applies to channel C1.* 607 608 Note that the network diagram has been simplified by replacing channel lines 609 with connection points, shown as blue circles which include the channel number. 610 No information has been lost. This representation is more scalable because it 611 eliminates crossing lines. This allows us to more clearly represent larger 612 networks. We've achieved this simplification by focusing on the connection 613 points between components and a channel, rather than the channel itself. 614 615 ## Adding another consortium definition 616 617 In this next phase of network development, we introduce organization R3. We're 618 going to give organizations R2 and R3 a separate application channel which 619 allows them to transact with each other. This application channel will be 620 completely separate to that previously defined, so that R2 and R3 transactions 621 can be kept private to them. 622 623 Let's return to the network level and define a new consortium, X2, for R2 and 624 R3: 625 626 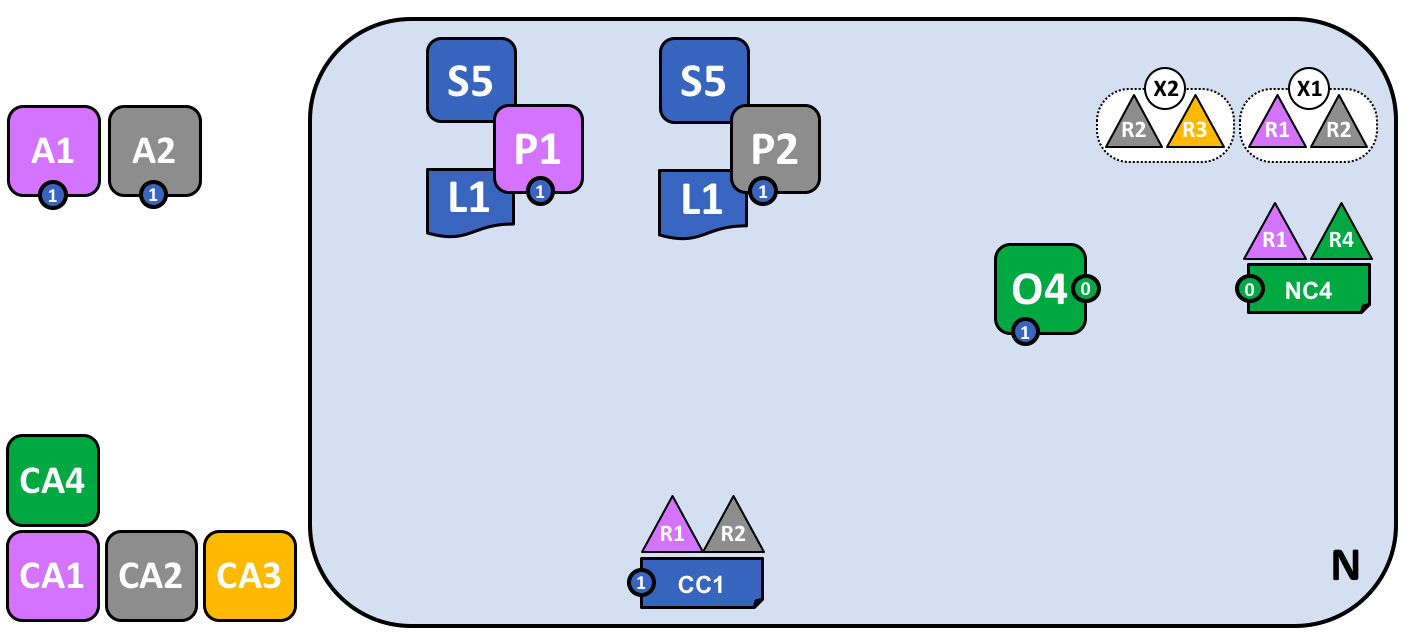 627 628 *A network administrator from organization R1 or R4 has added a new consortium 629 definition, X2, which includes organizations R2 and R3. This will be used to 630 define a new channel for X2.* 631 632 Notice that the network now has two consortia defined: X1 for organizations R1 633 and R2 and X2 for organizations R2 and R3. Consortium X2 has been introduced in 634 order to be able to create a new channel for R2 and R3. 635 636 A new channel can only be created by those organizations specifically identified 637 in the network configuration policy, NC4, as having the appropriate rights to do 638 so, i.e. R1 or R4. This is an example of a policy which separates organizations 639 that can manage resources at the network level versus those who can manage 640 resources at the channel level. Seeing these policies at work helps us 641 understand why Hyperledger Fabric has a sophisticated **tiered** policy 642 structure. 643 644 In practice, consortium definition X2 has been added to the network 645 configuration NC4. We discuss the exact mechanics of this operation elsewhere in 646 the documentation. 647 648 ## Adding a new channel 649 650 Let's now use this new consortium definition, X2, to create a new channel, C2. 651 To help reinforce your understanding of the simpler channel notation, we've used 652 both visual styles -- channel C1 is represented with blue circular end points, 653 whereas channel C2 is represented with red connecting lines: 654 655  656 657 *A new channel C2 has been created for R2 and R3 using consortium definition X2. 658 The channel has a channel configuration CC2, completely separate to the network 659 configuration NC4, and the channel configuration CC1. Channel C2 is managed by 660 R2 and R3 who have equal rights over C2 as defined by a policy in CC2. R1 and 661 R4 have no rights defined in CC2 whatsoever.* 662 663 The channel C2 provides a private communications mechanism for the consortium 664 X2. Again, notice how organizations united in a consortium are what form 665 channels. The channel configuration CC2 now contains the policies that govern 666 channel resources, assigning management rights to organizations R2 and R3 over 667 channel C2. It is managed exclusively by R2 and R3; R1 and R4 have no power in 668 channel C2. For example, channel configuration CC2 can subsequently be updated 669 to add organizations to support network growth, but this can only be done by R2 670 or R3. 671 672 Note how the channel configurations CC1 and CC2 remain completely separate from 673 each other, and completely separate from the network configuration, NC4. Again 674 we're seeing the de-centralized nature of a Hyperledger Fabric network; once 675 channel C2 has been created, it is managed by organizations R2 and R3 676 independently to other network elements. Channel policies always remain separate 677 from each other and can only be changed by the organizations authorized to do so 678 in the channel. 679 680 As the network and channels evolve, so will the network and channel 681 configurations. There is a process by which this is accomplished in a controlled 682 manner -- involving configuration transactions which capture the change to these 683 configurations. Every configuration change results in a new configuration block 684 transaction being generated, and [later in this topic](#the-ordering-serivce), 685 we'll see how these blocks are validated and accepted to create updated network 686 and channel configurations respectively. 687 688 ### Network and channel configurations 689 690 Throughout our sample network, we see the importance of network and channel 691 configurations. These configurations are important because they encapsulate the 692 **policies** agreed by the network members, which provide a shared reference for 693 controlling access to network resources. Network and channel configurations also 694 contain **facts** about the network and channel composition, such as the name of 695 consortia and its organizations. 696 697 For example, when the network is first formed using the ordering service node 698 O4, its behaviour is governed by the network configuration NC4. The initial 699 configuration of NC4 only contains policies that permit organization R4 to 700 manage network resources. NC4 is subsequently updated to also allow R1 to manage 701 network resources. Once this change is made, any administrator from organization 702 R1 or R4 that connects to O4 will have network management rights because that is 703 what the policy in the network configuration NC4 permits. Internally, each node 704 in the ordering service records each channel in the network configuration, so 705 that there is a record of each channel created, at the network level. 706 707 It means that although ordering service node O4 is the actor that created 708 consortia X1 and X2 and channels C1 and C2, the **intelligence** of the network 709 is contained in the network configuration NC4 that O4 is obeying. As long as O4 710 behaves as a good actor, and correctly implements the policies defined in NC4 711 whenever it is dealing with network resources, our network will behave as all 712 organizations have agreed. In many ways NC4 can be considered more important 713 than O4 because, ultimately, it controls network access. 714 715 The same principles apply for channel configurations with respect to peers. In 716 our network, P1 and P2 are likewise good actors. When peer nodes P1 and P2 are 717 interacting with client applications A1 or A2 they are each using the policies 718 defined within channel configuration CC1 to control access to the channel C1 719 resources. 720 721 For example, if A1 wants to access the smart contract chaincode S5 on peer nodes 722 P1 or P2, each peer node uses its copy of CC1 to determine the operations that 723 A1 can perform. For example, A1 may be permitted to read or write data from the 724 ledger L1 according to policies defined in CC1. We'll see later the same pattern 725 for actors in channel and its channel configuration CC2. Again, we can see that 726 while the peers and applications are critical actors in the network, their 727 behaviour in a channel is dictated more by the channel configuration policy than 728 any other factor. 729 730 Finally, it is helpful to understand how network and channel configurations are 731 physically realized. We can see that network and channel configurations are 732 logically singular -- there is one for the network, and one for each channel. 733 This is important; every component that accesses the network or the channel must 734 have a shared understanding of the permissions granted to different 735 organizations. 736 737 Even though there is logically a single configuration, it is actually replicated 738 and kept consistent by every node that forms the network or channel. For 739 example, in our network peer nodes P1 and P2 both have a copy of channel 740 configuration CC1, and by the time the network is fully complete, peer nodes P2 741 and P3 will both have a copy of channel configuration CC2. Similarly ordering 742 service node O4 has a copy of the network configuration, but in a [multi-node 743 configuration](#the-ordering-service), every ordering service node will have its 744 own copy of the network configuration. 745 746 Both network and channel configurations are kept consistent using the same 747 blockchain technology that is used for user transactions -- but for 748 **configuration** transactions. To change a network or channel configuration, an 749 administrator must submit a configuration transaction to change the network or 750 channel configuration. It must be signed by the organizations identified in the 751 appropriate policy as being responsible for configuration change. This policy is 752 called the **mod_policy** and we'll [discuss it later](#changing-policy). 753 754 Indeed, the ordering service nodes operate a mini-blockchain, connected via the 755 **system channel** we mentioned earlier. Using the system channel ordering 756 service nodes distribute network configuration transactions. These transactions 757 are used to co-operatively maintain a consistent copy of the network 758 configuration at each ordering service node. In a similar way, peer nodes in an 759 **application channel** can distribute channel configuration transactions. 760 Likewise, these transactions are used to maintain a consistent copy of the 761 channel configuration at each peer node. 762 763 This balance between objects that are logically singular, by being physically 764 distributed is a common pattern in Hyperledger Fabric. Objects like network 765 configurations, that are logically single, turn out to be physically replicated 766 among a set of ordering services nodes for example. We also see it with channel 767 configurations, ledgers, and to some extent smart contracts which are installed 768 in multiple places but whose interfaces exist logically at the channel level. 769 It's a pattern you see repeated time and again in Hyperledger Fabric, and 770 enables Hyperledger Fabric to be both de-centralized and yet manageable at the 771 same time. 772 773 ## Adding another peer 774 775 Now that organization R3 is able to fully participate in channel C2, let's add 776 its infrastructure components to the channel. Rather than do this one component 777 at a time, we're going to add a peer, its local copy of a ledger, a smart 778 contract and a client application all at once! 779 780 Let's see the network with organization R3's components added: 781 782  783 784 *The diagram shows the facts relating to channels C1 and C2 in the network N as 785 follows: Client applications A1 and A2 can use channel C1 for communication 786 with peers P1 and P2, and ordering service O4; client applications A3 can use 787 channel C2 for communication with peer P3 and ordering service O4. Ordering 788 service O4 can make use of the communication services of channels C1 and C2. 789 Channel configuration CC1 applies to channel C1, CC2 applies to channel C2.* 790 791 First of all, notice that because peer node P3 is connected to channel C2, it 792 has a **different** ledger -- L2 -- to those peer nodes using channel C1. The 793 ledger L2 is effectively scoped to channel C2. The ledger L1 is completely 794 separate; it is scoped to channel C1. This makes sense -- the purpose of the 795 channel C2 is to provide private communications between the members of the 796 consortium X2, and the ledger L2 is the private store for their transactions. 797 798 In a similar way, the smart contract S6, installed on peer node P3, and defined 799 on channel C2, is used to provide controlled access to ledger L2. Application A3 800 can now use channel C2 to invoke the services provided by smart contract S6 to 801 generate transactions that can be accepted onto every copy of the ledger L2 in 802 the network. 803 804 At this point in time, we have a single network that has two completely separate 805 channels defined within it. These channels provide independently managed 806 facilities for organizations to transact with each other. Again, this is 807 de-centralization at work; we have a balance between control and autonomy. This 808 is achieved through policies which are applied to channels which are controlled 809 by, and affect, different organizations. 810 811 ## Joining a peer to multiple channels 812 813 In this final stage of network development, let's return our focus to 814 organization R2. We can exploit the fact that R2 is a member of both consortia 815 X1 and X2 by joining it to multiple channels: 816 817  818 819 *The diagram shows the facts relating to channels C1 and C2 in the network N as 820 follows: Client applications A1 can use channel C1 for communication with peers 821 P1 and P2, and ordering service O4; client application A2 can use channel C1 822 for communication with peers P1 and P2 and channel C2 for communication with 823 peers P2 and P3 and ordering service O4; client application A3 can use channel 824 C2 for communication with peer P3 and P2 and ordering service O4. Ordering service O4 825 can make use of the communication services of channels C1 and C2. Channel 826 configuration CC1 applies to channel C1, CC2 applies to channel C2.* 827 828 We can see that R2 is a special organization in the network, because it is the 829 only organization that is a member of two application channels! It is able to 830 transact with organization R1 on channel C1, while at the same time it can also 831 transact with organization R3 on a different channel, C2. 832 833 Notice how peer node P2 has smart contract S5 installed for channel C1 and smart 834 contract S6 installed for channel C2. Peer node P2 is a full member of both 835 channels at the same time via different smart contracts for different ledgers. 836 837 This is a very powerful concept -- channels provide both a mechanism for the 838 separation of organizations, and a mechanism for collaboration between 839 organizations. All the while, this infrastructure is provided by, and shared 840 between, a set of independent organizations. 841 842 It is also important to note that peer node P2's behaviour is controlled very 843 differently depending upon the channel in which it is transacting. Specifically, 844 the policies contained in channel configuration CC1 dictate the operations 845 available to P2 when it is transacting in channel C1, whereas it is the policies 846 in channel configuration CC2 that control P2's behaviour in channel C2. 847 848 Again, this is desirable -- R2 and R1 agreed the rules for channel C1, whereas 849 R2 and R3 agreed the rules for channel C2. These rules were captured in the 850 respective channel policies -- they can and must be used by every 851 component in a channel to enforce correct behaviour, as agreed. 852 853 Similarly, we can see that client application A2 is now able to transact on 854 channels C1 and C2. And likewise, it too will be governed by the policies in 855 the appropriate channel configurations. As an aside, note that client 856 application A2 and peer node P2 are using a mixed visual vocabulary -- both 857 lines and connections. You can see that they are equivalent; they are visual 858 synonyms. 859 860 ### The ordering service 861 862 The observant reader may notice that the ordering service node appears to be a 863 centralized component; it was used to create the network initially, and connects 864 to every channel in the network. Even though we added R1 and R4 to the network 865 configuration policy NC4 which controls the orderer, the node was running on 866 R4's infrastructure. In a world of de-centralization, this looks wrong! 867 868 Don't worry! Our example network showed the simplest ordering service 869 configuration to help you understand the idea of a network administration point. 870 In fact, the ordering service can itself too be completely de-centralized! We 871 mentioned earlier that an ordering service could be comprised of many individual 872 nodes owned by different organizations, so let's see how that would be done in 873 our sample network. 874 875 Let's have a look at a more realistic ordering service node configuration: 876 877  878 879 *A multi-organization ordering service. The ordering service comprises ordering 880 service nodes O1 and O4. O1 is provided by organization R1 and node O4 is 881 provided by organization R4. The network configuration NC4 defines network 882 resource permissions for actors from both organizations R1 and R4.* 883 884 We can see that this ordering service completely de-centralized -- it runs in 885 organization R1 and it runs in organization R4. The network configuration 886 policy, NC4, permits R1 and R4 equal rights over network resources. Client 887 applications and peer nodes from organizations R1 and R4 can manage network 888 resources by connecting to either node O1 or node O4, because both nodes behave 889 the same way, as defined by the policies in network configuration NC4. In 890 practice, actors from a particular organization *tend* to use infrastructure 891 provided by their home organization, but that's certainly not always the case. 892 893 ### De-centralized transaction distribution 894 895 As well as being the management point for the network, the ordering service also 896 provides another key facility -- it is the distribution point for transactions. 897 The ordering service is the component which gathers endorsed transactions 898 from applications and orders them into transaction blocks, which are 899 subsequently distributed to every peer node in the channel. At each of these 900 committing peers, transactions are recorded, whether valid or invalid, and their 901 local copy of the ledger updated appropriately. 902 903 Notice how the ordering service node O4 performs a very different role for the 904 channel C1 than it does for the network N. When acting at the channel level, 905 O4's role is to gather transactions and distribute blocks inside channel C1. It 906 does this according to the policies defined in channel configuration CC1. In 907 contrast, when acting at the network level, O4's role is to provide a management 908 point for network resources according to the policies defined in network 909 configuration NC4. Notice again how these roles are defined by different 910 policies within the channel and network configurations respectively. This should 911 reinforce to you the importance of declarative policy based configuration in 912 Hyperledger Fabric. Policies both define, and are used to control, the agreed 913 behaviours by each and every member of a consortium. 914 915 We can see that the ordering service, like the other components in Hyperledger 916 Fabric, is a fully de-centralized component. Whether acting as a network 917 management point, or as a distributor of blocks in a channel, its nodes can be 918 distributed as required throughout the multiple organizations in a network. 919 920 ### Changing policy 921 922 Throughout our exploration of the sample network, we've seen the importance of 923 the policies to control the behaviour of the actors in the system. We've only 924 discussed a few of the available policies, but there are many that can be 925 declaratively defined to control every aspect of behaviour. These individual 926 policies are discussed elsewhere in the documentation. 927 928 Most importantly of all, Hyperledger Fabric provides a uniquely powerful policy 929 that allows network and channel administrators to manage policy change itself! 930 The underlying philosophy is that policy change is a constant, whether it occurs 931 within or between organizations, or whether it is imposed by external 932 regulators. For example, new organizations may join a channel, or existing 933 organizations may have their permissions increased or decreased. Let's 934 investigate a little more how change policy is implemented in Hyperledger 935 Fabric. 936 937 The key point of understanding is that policy change is managed by a 938 policy within the policy itself. The **modification policy**, or 939 **mod_policy** for short, is a first class policy within a network or channel 940 configuration that manages change. Let's give two brief examples of how we've 941 **already** used mod_policy to manage change in our network! 942 943 The first example was when the network was initially set up. At this time, only 944 organization R4 was allowed to manage the network. In practice, this was 945 achieved by making R4 the only organization defined in the network configuration 946 NC4 with permissions to network resources. Moreover, the mod_policy for NC4 947 only mentioned organization R4 -- only R4 was allowed to change this 948 configuration. 949 950 We then evolved the network N to also allow organization R1 to administer the 951 network. R4 did this by adding R1 to the policies for channel creation and 952 consortium creation. Because of this change, R1 was able to define the 953 consortia X1 and X2, and create the channels C1 and C2. R1 had equal 954 administrative rights over the channel and consortium policies in the network 955 configuration. 956 957 R4 however, could grant even more power over the network configuration to R1! R4 958 could add R1 to the mod_policy such that R1 would be able to manage change of 959 the network policy too. 960 961 This second power is much more powerful than the first, because R1 now has 962 **full control** over the network configuration NC4! This means that R1 can, in 963 principle remove R4's management rights from the network. In practice, R4 would 964 configure the mod_policy such that R4 would need to also approve the change, or 965 that all organizations in the mod_policy would have to approve the change. 966 There's lots of flexibility to make the mod_policy as sophisticated as it needs 967 to be to support whatever change process is required. 968 969 This is mod_policy at work -- it has allowed the graceful evolution of a basic 970 configuration into a sophisticated one. All the time this has occurred with the 971 agreement of all organization involved. The mod_policy behaves like every other 972 policy inside a network or channel configuration; it defines a set of 973 organizations that are allowed to change the mod_policy itself. 974 975 We've only scratched the surface of the power of policies and mod_policy in 976 particular in this subsection. It is discussed at much more length in the policy 977 topic, but for now let's return to our finished network! 978 979 ## Network fully formed 980 981 Let's recap what our network looks like using a consistent visual vocabulary. 982 We've re-organized it slightly using our more compact visual syntax, because it 983 better accommodates larger topologies: 984 985 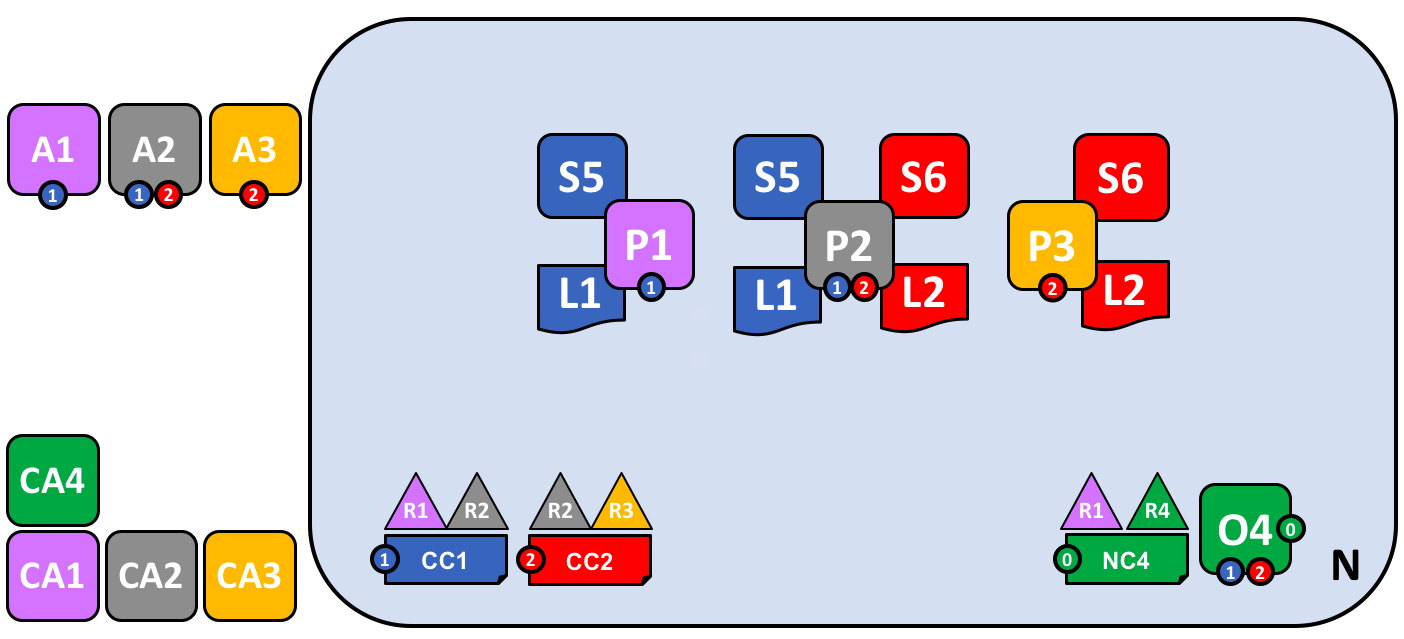 986 987 *In this diagram we see that the Fabric blockchain network consists of two 988 application channels and one ordering channel. The organizations R1 and R4 are 989 responsible for the ordering channel, R1 and R2 are responsible for the blue 990 application channel while R2 and R3 are responsible for the red application 991 channel. Client applications A1 is an element of organization R1, and CA1 is 992 it's certificate authority. Note that peer P2 of organization R2 can use the 993 communication facilities of the blue and the red application channel. Each 994 application channel has its own channel configuration, in this case CC1 and 995 CC2. The channel configuration of the system channel is part of the network 996 configuration, NC4.* 997 998 We're at the end of our conceptual journey to build a sample Hyperledger Fabric 999 blockchain network. We've created a four organization network with two channels 1000 and three peer nodes, with two smart contracts and an ordering service. It is 1001 supported by four certificate authorities. It provides ledger and smart contract 1002 services to three client applications, who can interact with it via the two 1003 channels. Take a moment to look through the details of the network in the 1004 diagram, and feel free to read back through the topic to reinforce your 1005 knowledge, or go to a more detailed topic. 1006 1007 ### Summary of network components 1008 1009 Here's a quick summary of the network components we've discussed: 1010 1011 * [Ledger](../glossary.html#ledger). One per channel. Comprised of the 1012 [Blockchain](../glossary.html#block) and 1013 the [World state](../glossary.html#world-state) 1014 * [Smart contract](../glossary.html#smart-contract) (aka chaincode) 1015 * [Peer nodes](../glossary.html#peer) 1016 * [Ordering service](../glossary.html#ordering-service) 1017 * [Channel](../glossary.html#channel) 1018 * [Certificate Authority](../glossary.html#hyperledger-fabric-ca) 1019 1020 ## Network summary 1021 1022 In this topic, we've seen how different organizations share their infrastructure 1023 to provide an integrated Hyperledger Fabric blockchain network. We've seen how 1024 the collective infrastructure can be organized into channels that provide 1025 private communications mechanisms that are independently managed. We've seen 1026 how actors such as client applications, administrators, peers and orderers are 1027 identified as being from different organizations by their use of certificates 1028 from their respective certificate authorities. And in turn, we've seen the 1029 importance of policy to define the agreed permissions that these organizational 1030 actors have over network and channel resources.