github.com/pachyderm/pachyderm@v1.13.4/doc/docs/1.10.x/enterprise/saml.md (about) 1 # Overview 2 3 This guide walks you through an example of using Pachyderm's SAML support, including the 4 following: 5 6 1. Activate Pachyderm enterprise and Pachyderm auth. 7 2. Configure Pachyderm's auth system to enable its SAML ACS, receive SAML 8 assertions, and allow you to log in by using the Okta® access management 9 software. 10 3. Log in to both the dash and CLI. 11 12 ## Activation 13 14 When starting out, we **highly** recommend running Pachyderm in Minikube, as 15 mistakes in this configuration could lock you out of your cluster. 16 17 To activate Pachyderm enterprise and Pachyderm auth: 18 19 ``` 20 pachctl enterprise activate <enterprise code> 21 pachctl auth activate --initial-admin=robot:admin 22 ``` 23 24 At this point, Pachyderm is ready to authenticate & authorize users. 25 26 What the `--initial-admin` flag does is this: 27 1. Pachyderm requires there to be at least one cluster admin if auth is 28 activated 29 2. Pachyderm's authentication is built around GitHub by default. Without this 30 flag, Pachyderm asks the caller to go through an OAuth flow with GitHub, and 31 then at the conclusion, makes the caller the cluster admin. Then whoever 32 activated Pachyderm's auth system can modify it by re-authenticating via 33 GitHub and performing any necessary actions 34 3. To avoid the OAuth flow, though, it's also possible to make the initial 35 cluster admin a "robot user". This is what 36 `--initial-admin=robot:<something>` does. 37 4. Pachyderm will print out a Pachyderm token that authenticates the holder as 38 this robot user. At any point, you can authenticate as this robot user by 39 running the following command: 40 41 ```shell 42 pachctl auth use-auth-token 43 ``` 44 45 **System response:** 46 47 ```shell 48 Please paste your Pachyderm auth token: 49 <paste robot token emitted by "pachctl auth activate --initial-admin=robot:admin"> 50 # you are now robot:admin, cluster administrator 51 ``` 52 53 The rest of this example assumes that your Pachyderm cluster is running in 54 minikube, and you're accessing it via `pachctl`'s port forwarding. Many of the 55 SAML service provider URLs below are set to some variation of `localhost`, 56 which will only work if you're using port forwarding and your browser is able 57 to access Pachyderm via `localhost` on the port forwarder's usual ports. 58 59 ## Create IdP test app 60 The ID provider (IdP) that this example uses is Okta. Here is an example 61 configuration for an Okta test app that authenticates Okta users 62 with Pachyderm: 63 64 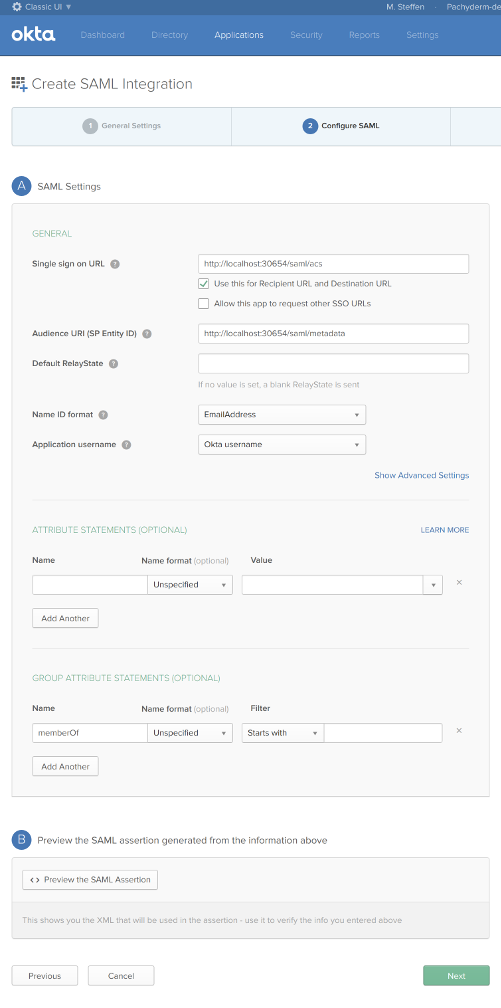 65 66 Once created, you can get the IdP Metadata URL associated with the test Okta 67 app here: 68 69 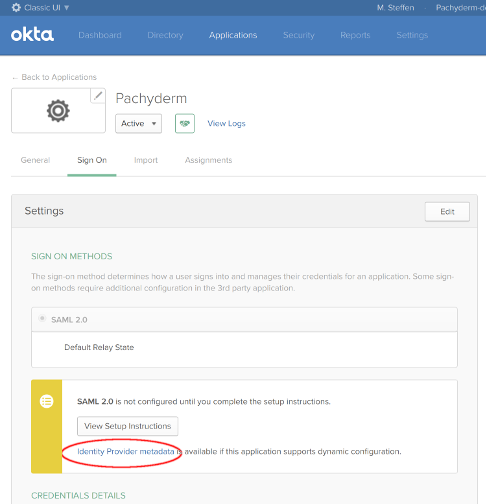 70 71 ## Write Pachyderm config 72 Broadly, setting an auth config is what enables SAML in Pachyderm 73 (specifically, it enables Pachyderm's ACS). Below is an example config that will 74 allow users to authenticate in your Pachyderm cluster using the Okta app above. 75 Note that this example assumes 76 77 ``` 78 # Lookup current config version--pachyderm config has a barrier to prevent 79 # read-modify-write conflicts between admins 80 live_config_version="$(pachctl auth get-config | jq .live_config_version)" 81 live_config_version="${live_config_version:-0}" 82 # Set the Pachyderm config 83 pachctl auth set-config <<EOF 84 { 85 # prevent read-modify-write conflicts by explicitly specifying live version 86 "live_config_version": ${live_config_version}, 87 "id_providers": [ 88 { 89 "name": "okta", 90 "description": "Okta test app", 91 "saml": { 92 "metadata_url": <okta app metadata URL>, 93 "group_attribute": "memberOf" # optional: enable group support 94 } 95 } 96 ], 97 "saml_svc_options": { 98 # These URLs work if using pachctl port-forward 99 "acs_url": "http://localhost:30654/saml/acs", 100 "metadata_url": "http://localhost:30654/saml/metadata", 101 "dash_url": "http://localhost:30080/auth/autologin", 102 } 103 } 104 EOF 105 ``` 106 107 ## Logging In 108 Currently Pachyderm only supports IdP-initiated authentication. To proceed, 109 configure your Okta app to point to the Pachyderm ACS 110 (`http://localhost:30654/saml/acs` if using `pachctl`'s port forwarding), then 111 sign in via the new Okta app in your Okta dashboard. 112 113 After clicking on the test Okta app, your browser will do a SAML authentication 114 handshake with your pachyderm cluster, and you will arrive at your Pachyderm 115 dashboard fully authenticated. To log in with the Pachyderm CLI, get a One-Time 116 Password from the Pachyderm dash, and then run `pachctl auth login 117 --code=<one-time password>` in your terminal. 118 119 ### Groups 120 If your SAML ID provider supports setting group attributes, you can use groups to manage access in Pachyderm with the `"group_attribute"` in the IDProvider field of the auth config: 121 ``` 122 pachctl auth set-config <<EOF 123 { 124 ... 125 "id_providers": [ 126 { 127 ... 128 "saml": { 129 "group_attribute": "memberOf" 130 } 131 } 132 ], 133 } 134 EOF 135 ``` 136 137 Then, try: 138 ``` 139 pachctl create repo group-test 140 pachctl put file group-test@master -f some-data.txt 141 pachctl auth set group/saml:"Test Group" reader group-test 142 ``` 143 144 Elsewhere: 145 ``` 146 pachctl auth login --code=<auth code> 147 pachctl get file group-test@master:some-data.txt # should work for members of "Test Group" 148 ``` 149