github.com/vieux/docker@v0.6.3-0.20161004191708-e097c2a938c7/docs/swarm/how-swarm-mode-works/pki.md (about) 1 <!--[metadata]> 2 +++ 3 title = "How PKI works" 4 description = "How PKI works in swarm mode" 5 keywords = ["docker", "container", "cluster", "swarm mode", "node", "tls", "pki"] 6 [menu.main] 7 identifier="how-pki-work" 8 parent="how-swarm-works" 9 weight="5" 10 +++ 11 <![end-metadata]--> 12 13 # How PKI works in swarm mode 14 15 The swarm mode public key infrastructure (PKI) system built into Docker Engine 16 makes it simple to securely deploy a container orchestration system. The nodes 17 in a swarm use mutual Transport Layer Security (TLS) to authenticate, authorize, 18 and encrypt the communications between themselves and other nodes in the swarm. 19 20 When you create a swarm by running `docker swarm init`, the Docker Engine 21 designates itself as a manager node. By default, the manager node generates 22 itself a new root Certificate Authority (CA) along with a key pair to secure 23 communications with other nodes that join the swarm. If you prefer, you can pass 24 the `--external-ca` flag to specify a root CA external to the swarm. Refer to 25 the [docker swarm init](../../reference/commandline/swarm_init.md) CLI 26 reference. 27 28 The manager node also generates two tokens to use when you join additional nodes 29 to the swarm: one worker token and one manager token. Each token includes the 30 digest of the root CA's certificate and a randomly generated secret. When a node 31 joins the swarm, it uses the digest to validate the root CA certificate from the 32 remote manager. It uses the secret to ensure the node is an approved node. 33 34 Each time a new node joins the swarm, the manager issues a certificate to the 35 node that contains a randomly generated node id to identify the node under the 36 certificate common name (CN) and the role under the organizational unit (OU). 37 The node id serves as the cryptographically secure node identity for the 38 lifetime of the node in the current swarm. 39 40 The diagram below illustrates how worker manager nodes and worker nodes encrypt 41 communications using a minimum of TLS 1.2. 42 43 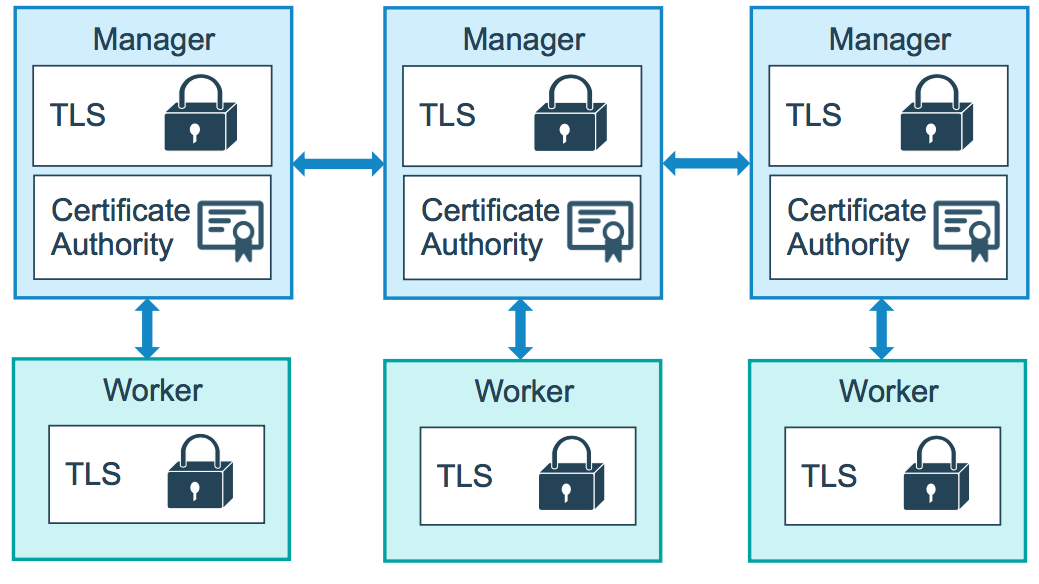 44 45 46 The example below shows the information from a certificate from a worker node: 47 48 ```bash 49 Certificate: 50 Data: 51 Version: 3 (0x2) 52 Serial Number: 53 3b:1c:06:91:73:fb:16:ff:69:c3:f7:a2:fe:96:c1:73:e2:80:97:3b 54 Signature Algorithm: ecdsa-with-SHA256 55 Issuer: CN=swarm-ca 56 Validity 57 Not Before: Aug 30 02:39:00 2016 GMT 58 Not After : Nov 28 03:39:00 2016 GMT 59 Subject: O=ec2adilxf4ngv7ev8fwsi61i7, OU=swarm-worker, CN=dw02poa4vqvzxi5c10gm4pq2g 60 ...snip... 61 ``` 62 63 By default, each node in the swarm renews its certificate every three months. 64 You can run `docker swarm update --cert-expiry <TIME PERIOD>` to configure the 65 frequency for nodes to renew their certificates. The minimum rotation value is 1 66 hour. Refer to the [docker swarm update](../../reference/commandline/swarm_update.md) 67 CLI reference. 68 69 ## Learn More 70 71 * Read about how [nodes](nodes.md) work. 72 * Learn how swarm mode [services](services.md) work.